Surveying the castle: New approaches to assessing Zero Trust Readiness Levels
In May, the Biden administration issued a sweeping executive order calling upon federal agencies to adopt a Zero Trust cybersecurity framework, and as a first step, develop plans within 60 days to adopt Zero Trust.
“Zero Trust” is a cybersecurity approach that moves defenses from static, network-based perimeters to focus on users, assets, and resources – in essence, it helps reduce the likelihood and impact of breaches by eliminating the concept of trust from an organization’s network architecture. Whereas traditional cybersecurity practices focus on a “castle and moat” model, where security protocols concentrate on keeping threats out, Zero Trust assumes that networks could be already breached, and requires continuous security validation.
Before an agency can create or adopt a plan to implement Zero Trust, however, it must first evaluate its cyber defense strategies to understand its gaps. The National Institute of Standards and Technology (NIST) outlined in 2020 a broad seven step process for migrating from a perimeter-based security architecture to Zero Trust Architecture that included such an assessment, but stopped short of providing a roadmap.
To fill that critical gap, leading experts at Leidos have developed the Zero Trust Readiness Level assessment, a tailored roadmap to better help agencies survey their castle and prepare for the transition to Zero Trust.
How Mature is Your Enterprise?
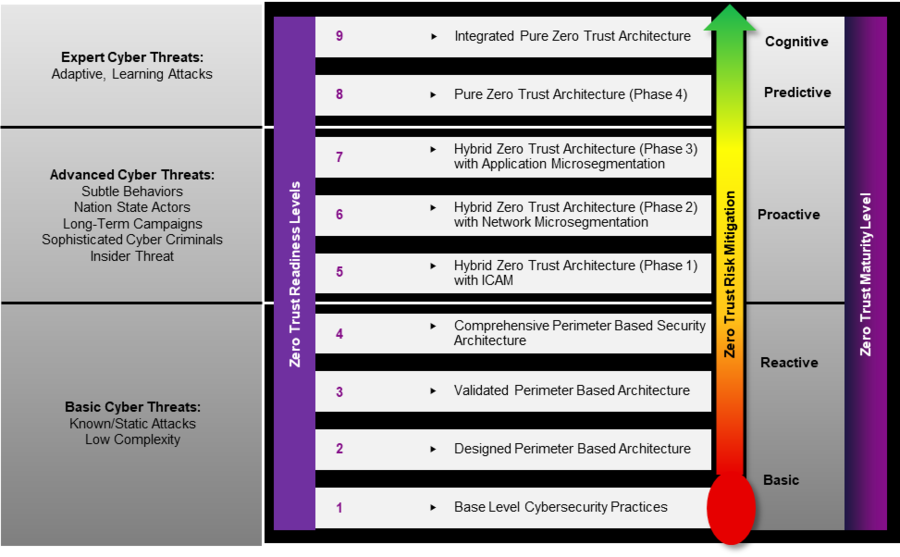
The Leidos Zero Trust Readiness Level pairs the level of protection to the evaluated threat risk, providing a scale with which organizations can measure their readiness against increasingly advanced cyber threats. But how to evaluate safeguards and threats?
The Leidos Zero Trust Readiness Level assists an enterprise in prioritizing cyber threats across two domains: the value of an enterprise’s mission and data, as well as the complexity of its network infrastructure. By and large, the more valuable the mission and data, and more complex the network, the higher risk of an attack.
Through these assessments, an enterprise can determine how best to implement required Zero Trust principles, maximize positive security impact, and minimize cost, schedule, and technical risk. And it can help assess what level of cyber threat an enterprise is ready to defend. Just follow the 1-9 scale.
Built upon existing the cybersecurity hygiene and compliance measures in place, the Leidos Zero Trust Readiness Level can baseline an enterprise’s cybersecurity posture and whether it’s ready to defend against basic, advanced, or expert attacks.
Leidos’ Zero Trust Readiness Level is based upon continued cyber hygiene and compliance best practices in accordance with certification and accreditation requirements. Compliance practices that authorize a system based on selecting, implementing, assessing and monitoring security controls affords protection against static attacks and other basic cyber threats. Under Leidos’ framework, an enterprise can then iteratively build cybersecurity maturity that provides direct protection against more advanced threats, before eventually, implementing an integrated pure zero trust architecture protective against even expert cyber threats.