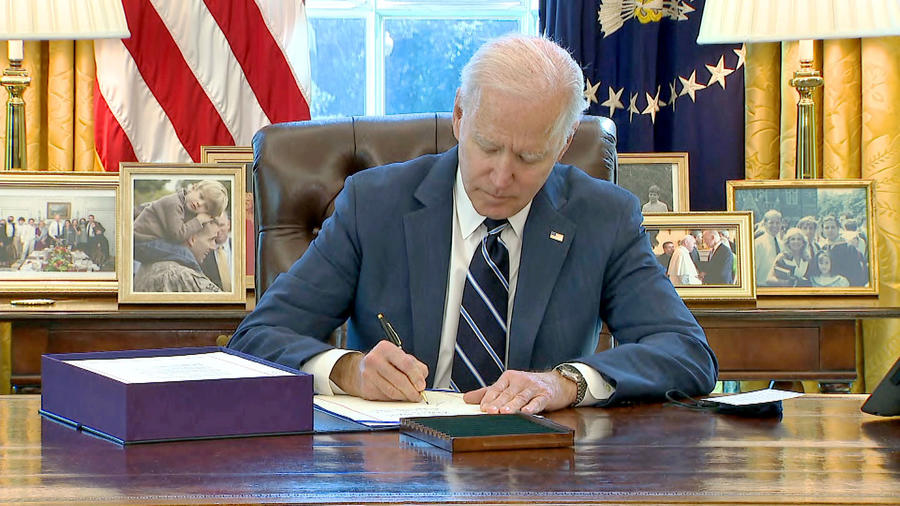
The Biden Cyber Executive Order: What’s happened in the first 60 days?
This week, federal agencies crossed the first threshold to take action on President Biden’s Executive Order (EO) on cybersecurity signed in May. This first phase gave federal agencies 60 days from the date of signing to prepare updated plans toward the adoption of cloud technology pursuant to relevant OMB guidance. These plans must also include a plan to adopt Zero Trust Architecture as outlined by National Institute of Standards and Technology (NIST) standards. In agencies’ updated plans, they’re asked to include any steps they’ve already taken towards any requirement in the EO, point out any activity that’s likely to have the most immediate security impact, and include a schedule toward implementing all other requirements listed in the EO. Finally, agencies had until July 12 (60 days) from the signing to submit reports detailing their plans to the Director of Office of Management and Budget (OMB) and Assistant to President and National Security Advisor (APNSA).
While most of the focus in the analysis of the EO has centered on the impact to federal agencies scattered around the beltway and across the country, the executive branch has not let itself off the hook in terms of required actions these first 60 days. In the spirit of improving information sharing between the public and private sector as well as intra-government collaboration, the EO requires that the Director of OMB, in consultation with the Secretary of Defense, Attorney General, Secretary of Homeland Security, and Director of National Intelligence, will review the Federal Acquisition Requirement (FAR) and the Defense Federal Acquisition contract requirements. Put more plainly; these executive agencies are mandated to meet and review the FAR and related legislation to examine how private IT providers communicate with the government with four main objectives in mind:
- To ensure service providers capture and save all process records and data as it relates to cybersecurity protection as well as recovery efforts in the event of a breach.
- To require service providers to share this type of data with any relevant government agency in the event of a cyber incident or near incident.
- To ensure service providers collaborate with federal cybersecurity professionals in their investigations and responses to breaches or other cyber incidents.
- To ensure that service providers share all cyber incident documentation in industry-standard reporting formats.
So let’s discuss how agencies have worked through the first 60 days, how they’ve met the requirements, and what challenges they see going forward. The consensus among industry observers has primarily been categorized in three phases over these first 60 days.
Challenge Issued
First, agencies immediately recognized that they had just been handed a major challenge that would ultimately revolutionize the way they approach cybersecurity. While a cyber-centric EO coming early in the Biden administration was no major surprise to industry observers, it would not have been possible to plan for all the specific mandates or timelines in the EO. Our team has fielded numerous calls from agency technical leaders to discuss the path forward and address occasional uncertainties around meeting these requirements on time. Fortunately, Leidos’ portfolio of capabilities, our decades of experience, and relationships in both public and private sectors give us a unique ability to help these agencies understand the value of what they may already have in place and begin making a plan to fill in the gaps.
Challenge Accepted
The second phase has naturally been a transitional one where agencies began to feel more confident with their own internal ability to execute on these new requirements and understand the support capabilities available from the private sector. What’s more, the government itself has issued helpful guidelines along the way to help agencies plan, for example, NIST’s definition of critical software and a Zero Trust adoption plan published earlier this year by NSA. Agencies in this stage began to weigh the benefits of sharing their plans with outside partners like Leidos for input and advice or going it alone with their 60-day plan before submission.
Dollars and Sense
Finally, the third phase seems to have been a new period of uncertainty around funding. Many agencies embraced the scope and timeline of the requirements in the EO, then gained even more confidence once they started to “put pen to paper” with a plan for modernization, but more recently they’ve been faced with the question of where the funding will come from. While the White House did issue a request for $750 million to be spent on cybersecurity in fiscal 2022, the administration has not yet specified where exactly that funding will go. If the bulk, or even the entirety of that $750 million, is earmarked for cyber initiatives related to the EO, that is certainly a positive. But even in that case, it’s unlikely to be enough to make good on the sweeping requirements found throughout the order. So if this measure is to fully succeed, where is the rest of the money supposed to come from? The good news is there does seem to be strong bipartisan support in Congress for meaningful funding of cybersecurity measures. Look to Congress this summer as a key bellwether on how the funding issue will resolve as cyber hearings take place in both houses of Congress.
The next major threshold in the EO is just about 30 days away so stay tuned for more analysis of the three major waypoints to modern cybersecurity, and much more.
We invite you to read part one in our multipart series on the Executive Order: Unpacking President Biden's cybersecurity Executive Order